It happened fast. One quick scan, a few tapped digits on a slick-looking payment page, and I was back on the Strip thinking I had sorted my parking in under thirty seconds. Convenient, right? Wrong. Three weeks later, my credit card statement had a mystery charge with a name I had never seen before. That parking meter moment in Las Vegas turned out to be one of the most expensive thirty-second decisions I had ever made.
QR codes are everywhere now, and Las Vegas is no exception. Millions of tourists descend on the city every year, and most of them are moving fast, distracted, and trusting that the infrastructure around them is legitimate. That trust, it turns out, is exactly what criminals are counting on. Let’s dive in.
The Scam Has a Name, and It’s Spreading Like Wildfire

It’s called “quishing,” a blend of QR code and phishing, and it’s one of the fastest-growing fraud tactics in the country right now. The FBI identifies quishing as a rapidly spreading trap in public spaces. Honestly, I didn’t even know it had a proper name until after it happened to me.
Quishing attacks have skyrocketed by a factor of ten between 2021 and 2024, according to security company Egress. A tenfold increase. Let that sink in. That’s not a niche cybercrime trickling in from the shadows; that’s a full-blown epidemic playing out on city sidewalks near you.
Why a Parking Meter Is the Perfect Trap

QR codes are designed for convenience and speed. When you’re in a hurry, rushing to a meeting or trying to pay for parking before your meter expires, you’re more likely to scan without thinking. Criminals count on this urgency. Vegas, of all places, is tailor-made for this. You are perpetually late, perpetually distracted, and perpetually surrounded by strangers.
The brilliance of this scam lies in its simplicity. Criminals do not need to hack the parking meter’s software, nor do they need to install complex skimming devices. Instead, they simply print a sticker. They generate a QR code leading to a fake website that mimics the city’s official parking portal. No technical degree required. Just a printer and zero conscience.
Cities Across America Are Already Reporting Compromised Meters

Cities across America are reporting widespread QR code tampering on parking meters and payment stations. Austin discovered 29 compromised parking pay stations, Houston found fake codes at multiple locations, and New York City’s Department of Transportation issued urgent warnings about fraudulent codes on parking meters. Those are just the ones that got caught.
A new QR code parking scam was reported rising across Southern California, and Las Vegas was identified as a city that could possibly be hit next. Here’s the thing: Vegas is a premium target. Millions of visitors cycle through every month, most of them unfamiliar with local parking apps, most of them moving fast. That’s not a city that criminals skip. That’s a city they circle.
The Numbers Behind the Fraud Are Staggering
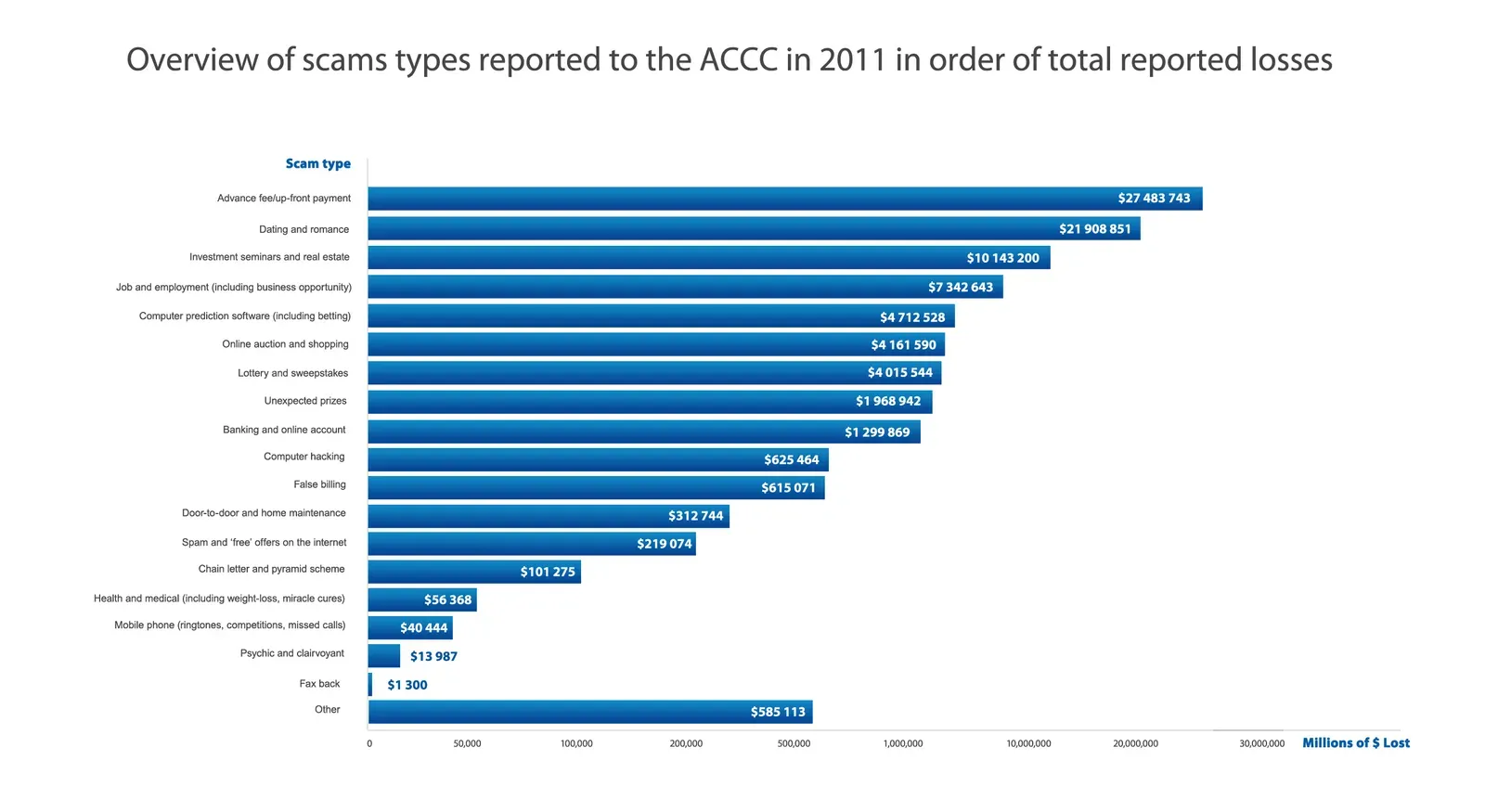
Newly released Federal Trade Commission data show that consumers reported losing more than $10 billion to fraud in 2023, marking the first time that fraud losses have reached that benchmark. Ten billion dollars. In a single year. That number is almost impossible to process.
Consumers reported losing $10 billion to scams and fraud in 2023, up from $9 billion the year before, according to the FTC. In 2020, Americans lost only $3.5 billion to fraud, including identity theft. The growth curve here is not subtle. It is nearly vertical, and QR code scams are feeding directly into it.
The Fake URL Trick Is Diabolically Simple

Scammers create QR code stickers that look just like the real deal. The crooks set up websites with names eerily similar to legitimate parking payment sites, for example, “PoyByPhone” instead of “PayByPhone.” One letter. One switched vowel. That is all it takes to redirect your credit card details to a criminal halfway around the world.
In Redondo Beach, California, parking meter inspectors discovered 150 stickers placed on meters that directed drivers to a “poy by phone” website, a misspelling that revealed the fraud. One hundred and fifty meters. Tampered. And that’s just one city in one summer. The scope of what is going unreported is something I find genuinely alarming.
Malware Risk: It Goes Way Beyond Stealing Your Card Number

Theft is not always just about stealing a credit card number for a one-time charge. Some malicious QR codes may attempt to install malware onto your smartphone. If successful, this software can sit silently in the background, potentially logging your keystrokes or accessing sensitive information. By the time you realize something is wrong, the damage is often extensive.
Nearly 90% of QR code attacks are aimed at stealing login information and other sensitive data. About 89.3% of detected attacks are done to capture personal data. We’re not talking about someone skimming a parking fee. We’re talking about full-scale credential harvesting, account takeovers, and in some cases identity fraud that can take years to untangle. That’s the version of the story nobody tells you at the parking meter.
The FBI and FTC Have Both Sounded the Alarm

The FBI’s Internet Crime Complaint Center has experienced an increase in complaints related to QR code phishing scams with rapid advancement between 2023 and 2025. Each day, restaurants, parking machines, event signs, product boxes, and charity collection points become locations of QR code phishing attacks. The FBI doesn’t issue public warnings about things that are rare or theoretical.
The increasing prevalence of QR code scams prompted a warning from the Federal Trade Commission about unwanted codes that when scanned “could take you to a phishing website that steals your personal information, like credit card numbers or usernames and passwords.” It could also download malware onto your phone and give hackers access to your device. Two of the most powerful consumer protection agencies in the country are saying the same thing. That’s worth paying attention to.
The QR Code’s Biggest Flaw: You Can’t Check the Link Before You Scan

The smart part for the criminals is that you can’t check the link first, as you do with normal web links. Think about that for a moment. With a regular hyperlink in an email, you can hover over it and see exactly where it leads. A QR code gives you no such preview. It’s a black box until you’ve already opened it.
The use of QR codes as phishing payloads rose from just 0.8% in 2021 to 12.4% in 2023, and sustained a high rate of 10.8% in 2024. Criminals are not experimenting with QR codes anymore. They have fully committed to the format precisely because of this visibility problem. It is a built-in vulnerability that is very hard to patch.
Real Victims, Real Damage: What the Patterns Actually Look Like

According to the BBB, victims of this scam often see a small amount charged to their card but typically don’t receive any proof of payment for parking. One victim reported a $1.98 charge that appeared shortly after using a QR code to pay for parking. Then a $49.99 charge showed up on the credit card each month for the next three months. Because the company wouldn’t respond, the victim eventually had to cancel the card entirely to stop the unauthorized payments.
In one case at a UK car park, fraudsters overlaid genuine QR codes with their own, redirecting users to phishing sites. One victim suffered catastrophic consequences, including direct financial theft through unauthorized loans and credit card applications in their name. The victim incurred debts totaling £13,000, including a fraudulent loan of £7,500 taken out by the scammers. This case illustrates how QR code scams can go far beyond simple payment theft to full-scale identity fraud with long-lasting financial consequences. That is a life-altering outcome from a parking meter. I know it sounds unbelievable, but here we are.
How to Actually Protect Yourself (Starting Right Now)

If you see a QR code on a parking meter, run your finger over it. Ask yourself if it looks like a cheap sticker stuck on top of existing signage. If it feels raised, peels easily, or covers other text, ignore it. Better yet, do not scan it at all. Download the official parking app for your city directly from the App Store or Google Play.
Many parking operators provide official payment apps or websites. If in doubt, manually type the URL displayed on the meter instead of scanning a QR code. Ensure the website or app you’re using matches the parking operator’s official name and includes “https://” in the URL. Avoid platforms that look suspicious or request unnecessary information. Yes, typing a URL feels old-fashioned. It also feels a lot better than disputing $49.99 monthly charges and canceling your card on a Tuesday afternoon.
Conclusion: Vegas Will Eat You Alive If You’re Not Paying Attention

Las Vegas is built on distraction, speed, and the comfortable illusion of convenience. So is the quishing scam. The two fit together almost too perfectly. Every tourist in a hurry, every QR code that says “Scan to Pay,” every meter that looks slightly too polished – these are all potential traps now.
The data from the FBI, FTC, and independent cybersecurity researchers all point in the same direction. Quishing incidents are rising roughly a quarter year-over-year into 2025, and malicious QR codes have risen by a similar margin in 2025. This is not slowing down. If anything, it’s accelerating.
I’ll never scan . Not because I’m paranoid, but because I now know exactly how cheap and easy these traps are to set. Next time I see that little square on a meter, I’m downloading the official city app, typing in the URL manually, or paying the old-fashioned way. The thirty seconds I save are not worth what I might lose. What about you? Would you have spotted the fake?










